Enabling The Economy To Reopen

Blog Post by Ajay Madhok
mediaX Distinguished Visiting Scholar
One of the contagious side-effects of the pandemic is the debate on how the economy will play out in a post-corona world. Will the economic recovery look like U, V, W, or take a new form? Despite the particular experiment attempted in our part of the world, we all agree it will take more than washing our hands and moving on.
There is broad agreement that developing immunity is the only sustainable option, whether we do it medically through a vaccine, or by getting exposed to the virus and developing antibodies organically. There have been three approaches to managing the pandemic so far — the Herd Immunity strategy as championed by Sweden, the Enforced Quarantine program implemented by countries like China and New Zealand, and the Hammer & Dance here in the U.S.
Given COVID-19’s known unknowns and clinical mystique, it’s way too soon to state which model will perform better categorically. But, without a durable system in place, we may find ourselves trapped — waiting for the balance between saving lives and livelihoods. This paper proposes a decentralized approach that improves targeting social distancing measures combined with certified risk assessment. It is inspired by the simplicity and usability of contactless mobile payments and leverages the internet-scale, secure peer-to-peer transactions infrastructure.
1. POLICY AND TECHNOLOGY CAPABILITY
While Policy can direct the critical pre-conditions required before reopening of the economy, can we be ready with the Technology Capability when R0 (the Basic Reproduction Number) goes below 1? Won’t we need more than just the widespread availability of personal protection equipment and unrestricted availability of Tests to get going even with a new normal? Today, we have an opportunity to design the essential technology to facilitate the reopening of the economy, before the virus has run its course, and contribute to a widely available solution.
It has been most inspiring to see Apple and Google collaborate on Contact Tracing. Introducing it at the Operating System level will enable adoption and scale. The backbone of any solution that enables communities to return to their business-as-usual will build upon the Antibody and other Tests on individuals, and Contact Tracing at large. While necessary to flatten the curve, they are not sufficient to reopen the economy. What is missing is a solution that enables a business to make the critical decision to let people back in confidently. A peer-to-peer trust infrastructure that provides the economy a force multiplier without compromising our privacy.
2. APPROACH
Here is an overview of a solution approach that leverages two complementary strategies — targeting social distancing more precisely, and using predictions to prevent its transmission. Testing and Contact Tracing thus become the means towards the end goal of safely allowing entry and commingling in physical spaces, facilitating the economy to reopen.
What if we enable anyone to make a claim about their health condition with the same ease and breadth as using a Driver’s License to assert their name or age. Today, when a person presents their License at a hotel reception, the check-in staff verifies the person’s identity by matching their picture on the License. If it matches, they accept the name and age on the License, operating as a Relying Party, trusting that DMV, the Issuing Authority has verified those claims.
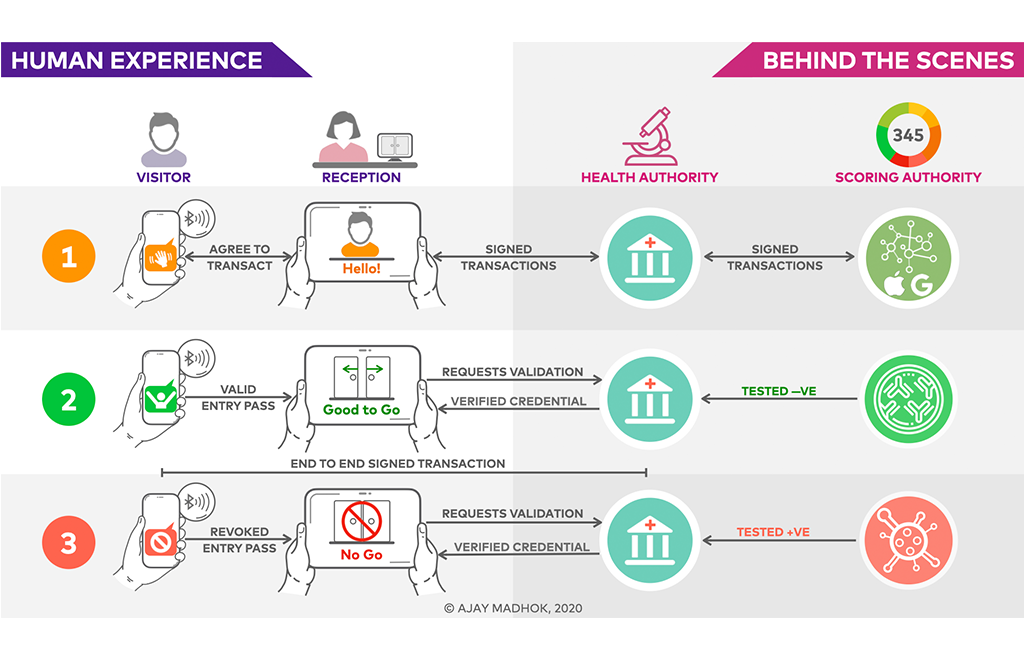
2.1 EXPERIENCE
A Visitor uses their smartphone to present a Digital Entry Pass, to the person or the kiosk at the reception to assert they are healthy. The business uses a Visitor Surety product code-named, Safe Haven, to validate its authenticity and claim from the Issuer, the Health Authority. The QR code on the Entry Pass provides the Go/No-Go decision to the business without revealing the Visitor’s identity, or their Score or Risk. If the Visitor was tested positive, they are in Red State and Green indicates they were tested negative, or conferred immunity through vaccination, a past infection, or a treatment. Visitors verified Green are allowed entry, while others guided to get the help they need, and their needs accommodated while keeping others safe.
Each transaction is digitally signed using public/private certificates issued to the Visitor’s smartphone. Visitors could get their Entry Pass before visiting the business, much like obtaining a digital boarding pass before leaving for the airport. Sent to their smartphone, the Entry Pass is added to the mobile wallet to limit the data that needs to be exposed when used.
The Scoring Authority computes the Health Score for people who have opted-in. The Score is a continuum that is updated continuously based on our social distancing behaviors. It is lower for someone who gets exposed to an infectious area or infected people, and higher if they were isolated, or treated of their infection, or immunized. For example, the Score will slowly go up if we were sheltering in place and go down if we start to see many people. The Health Authority determines the Score Range and thresholds for safe passage to a facility based on the kind of business and its community. For example, access to a senior living facility might require a score of 950 (out of 1000), while a grocery store might require a score of 700. It is similar to a lender obtaining the borrower’s Credit Score from a Credit Bureau to make their lending decision.
2.2 BEHIND THE SCENES
The Scoring Authority is built on the Exposure Notifications capability contributed by Apple and Google. It uses temporary exposure keys to determine an opted-in person’s proximity to someone who has a confirmed or potential exposure to the virus. It identifies them as affected and shares their diagnosis keys to alert other users to potential exposure. Individuals voluntarily submit their test results from certified Test Labs and Public Authorities, and Front-line agencies submit reports on contaminated areas. Once verified, the Health Authority updates the Scoring Authority, which in turn notifies people it predicts to be at risk. Initially, a classic Expert System with simple heuristics computes the Score and Risk levels to ensure explainability. Over time, as testing becomes generally available, we can offer more data to machine learning algorithms to make better predictions on exposure and transmission risks.
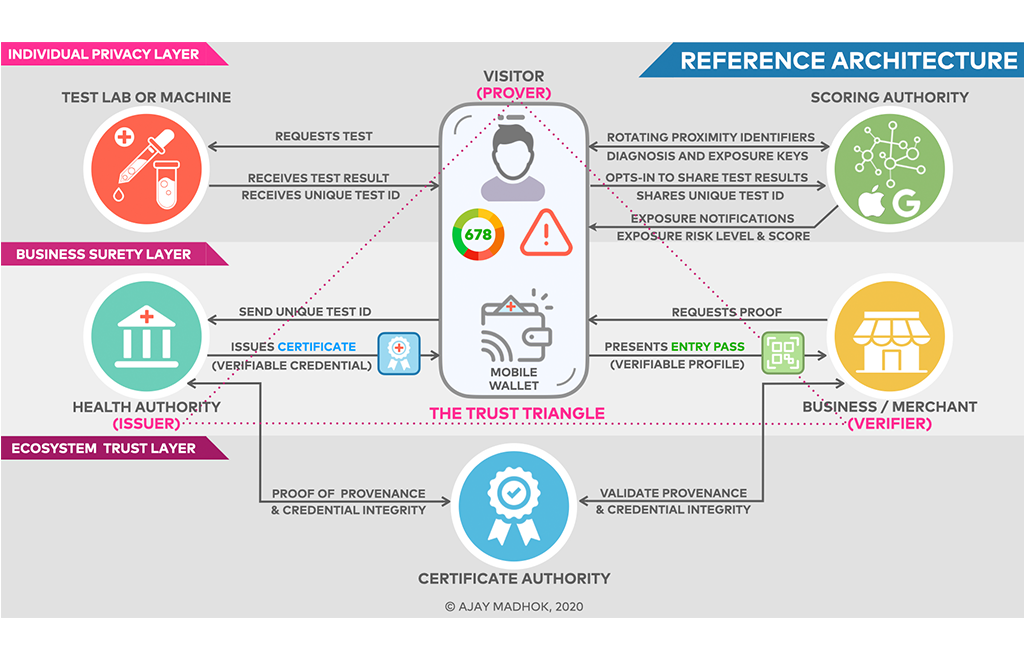
3. REFERENCE ARCHITECTURE
The architecture provides a means for any individual or business to establish peer-to-peer Trust over the Internet. By using crypto-verifiable digital credentials, it enables us to present our claims, and businesses to verify them without requiring any intermediaries. It leverages Exposure Notifications and internet foundations such as TLS, PKI, and Certificate Authority.
It enables a person (Prover) to present their Verifiable Credentials, such as their driver’s license, qualifications, or health data over the Internet while protecting their privacy. They obtain the Proof from an Issuer (Health Authority) in the form of a Health Certificate and store it in their Mobile Wallet. They use it to present a Verifiable Profile in the form of an Entry Pass to the business (Verifier), who verifies its ownership and claims from the Issuer to grant entry. In practice, the Visitor can obtain a Certificate from the issuing Health Authority in advance. The Certificate contains specific claims such as their test results and metadata including the issue and expiry date. The Health Authority can revoke it anytime if the person’s score or risk changes.
3.1 INDIVIDUAL PRIVACY LAYER
This layer enables anyone to get Exposure Notifications from the Scoring Authority. Once they are opted-in, the Safe Haven Individual App uses Rotating Proximity Identifiers to receive exposure notifications, health score, and transmission risk levels. A person can use the App to request a test from a certified Test Lab, or a Test Machine, and share the test results with the Scoring Authority using a unique Test ID. A test can confirm if they have the virus (tested +Ve), or have developed antibodies that confer immunity (tested -Ve). The App can be used to get a Health Certificate and generate a digitally signed Entry Pass, which is a Verifiable Profile.
3.2 BUSINESS SURETY LAYER
This layer enables trusted interactions using Verifiable Credentials between a Visitor (Prover), a Business (Verifier), and the Health Authority (Issuer). A Business uses the Safe Haven Business App to request Proof that the Visitor is healthy, and the Visitor presents their Entry Pass as the Proof using their mobile wallet. The Business is responsible for verifying the authenticity and provenance of the Entry Pass presented by the Visitor. Once verified, it gets the surety to allow entry to the Visitor. They only get to know if the visitor is cleared, but not their identity.
3.3 ECOSYSTEM TRUST LAYER
The Ecosystem Trust layer provides the cryptographic means by which any two peers (software agents or apps) can securely communicate in the Trust Triangle of the Issuer, Prover, and the Verifier. They can request and consume verifiable credentials to support specific Trust policies of their particular environment. It thus enables consistent user experience of trust decisions across the ecosystem, making it possible for the solution to scale.
This layer interoperates with a Certificate Authority and provides a governance framework defining the principles and the policies that apply to all entities in the ecosystem. A similar model exists for the most successful physical credentials we use every day — passports, driving licenses, and credit cards. It has enabled the largest trust networks like Mastercard to scale.
Over time, we can replace Rotating Proximity Identifiers with Decentralized Identifiers, the cryptographically secure, privacy-respecting, and machine-verifiable identifications. The Ecosystem Layer can be enhanced with ZKP-based credentials to comply with GDPR and similar data protection regulations. Smart Contracts and Distributed Ledger can be leveraged to support public validation of private data (credentials) without the need to store that data.
4. IT’S TIME TO BUILD
A large tech company like Apple, Google, Microsoft, or Facebook is in the best position to develop the proposed Safe Haven capabilities. Digital Trust over the Internet will empower any real-world business to rebuild trust with their community by assuring that they are contagion free. Enabling people to assert their health and immunity in a manner that does not breach their privacy or hurt personal sensibilities will help adoption.
The reference architecture provides the rules and the tools for responsive coordination at scale, building on existing capabilities to make it achievable in the short term, and sustainable in the long run. From a commercial perspective, the solution can be productized and licensed for free to government facilities such as airports, schools, courts, and small businesses like small stores and restaurants. Enterprises such as Airlines, Hotels, and Resorts are charged a subscription fee.
5. WHY NOW?
We are on a path to flatten the curve to prevent the catastrophe that would occur if hospitals were to overrun. Although it is the only safe option today, shutting the society down will prolong the time to get to herd immunity. It creates a situation where we now must wait for a vaccine, an indefinite period between when the spread of infection has slowed and availability of a vaccine or treatment. We want to reopen the economy safely while we wait for a vaccine.
There has never been a more critical time to orchestrate solution efforts for a grand challenge. We can create a solution today that provides a more rigorous path for the economy to reopen. And by demanding more from each other, we can contribute to the technology capability that will enable cities, states, and nations to build the future. I would love to be a part of it.
The attached FAQ document is an invitation to provide answers to the questions this will raise. Thank you for your contributions.
 Ajay Madhok is a growth architect and the Founding Partner of Reboot Digital. Having experienced innovation from both sides by helping grown-ups innovate and building startups to disrupt them, Ajay’s expertise is in translating good ideas into successful new products. He is fascinated by corporate innovation models, and his research focus is on organizational resilience through perpetual renewal. The purpose-built startup is one such model that draws on his experience in combining foundational assets of an enterprise with startup talent to create new growth vehicles. Ajay builds startups, advises venture funds, and consults with large corporations to amplify their innovations efforts. He is an advisor to Playground Global and a member of the technology advisory council of Harman International. He earned his B.S. degree in Electrical and Electronics Engineering, and an M.S. degree in Mathematics from the Birla Institute of Technology and Science, Pilani, India.
Ajay Madhok is a growth architect and the Founding Partner of Reboot Digital. Having experienced innovation from both sides by helping grown-ups innovate and building startups to disrupt them, Ajay’s expertise is in translating good ideas into successful new products. He is fascinated by corporate innovation models, and his research focus is on organizational resilience through perpetual renewal. The purpose-built startup is one such model that draws on his experience in combining foundational assets of an enterprise with startup talent to create new growth vehicles. Ajay builds startups, advises venture funds, and consults with large corporations to amplify their innovations efforts. He is an advisor to Playground Global and a member of the technology advisory council of Harman International. He earned his B.S. degree in Electrical and Electronics Engineering, and an M.S. degree in Mathematics from the Birla Institute of Technology and Science, Pilani, India.